Generate New Ssh Key Kali
Generate Ssh Key Windows
To setup SSH keys between two servers we need to follow these steps:
- Jan 06, 2019 Remember, for each device you must generate a different public & private key, save the private key on the same device you want to ssh from, copy the public key into the authorizedkeys file.
- I am trying to set up my Pi 3 B+ with kali linux to create a test box to practice some attacks. I am following these tutorials: Set Up an Ethical Hacking Kali Linux Kit on the Raspberry Pi 3 B+; Build a Beginner Hacking Kit with the Raspberry Pi 3 Model B+; Everything has been fine until I came to the part where I need to generate new SSH keys.
- The following command creates an SSH key pair using RSA encryption and a bit length of 4096: ssh-keygen -m PEM -t rsa -b 4096 If you use the Azure CLI to create your VM with the az vm create command, you can optionally generate SSH public and private key files using the -generate-ssh-keys option.
Creating a new key pair for authentication. To create a new key pair, select the type of key to generate from the bottom of the screen (using SSH-2 RSA with 2048 bit key size is good for most people; another good well-known alternative is ECDSA). Then click Generate, and start moving the mouse within the Window. Putty uses mouse movements to. PuTTYgen is an key generator tool for creating SSH keys for PuTTY. It is analogous to the ssh-keygen tool used in some other SSH implementations. The basic function is to create public and private key pairs. PuTTY stores keys in its own format in.ppk files. However, the tool can also convert keys to and from other formats. Jan 06, 2019 Remember, for each device you must generate a different public & private key, save the private key on the same device you want to ssh from, copy the public key into the authorizedkeys file.
Create a key pair on the source server. When we give ssh-keygen command, it will by default create a 2048 -bit RSA Key pair and if you need more stronger encryption you can use 4096 bit as well. For that you need to use “-b 4096” in the ssh-keygen command end. I am using default one here.
The next section shows a full example of what each key file should look like. The Generated Key Files. The generated files are base64-encoded encryption keys in plain text format. If you select a password for your private key, its file will be encrypted with your password. Be sure to remember this password or the key pair becomes useless.
Couple of things to be taken care in the below output:
 Generate major keys to success with Khaled Ipsum, the best DJ Khaled Lorem Ipsum placeholder text generator.
Generate major keys to success with Khaled Ipsum, the best DJ Khaled Lorem Ipsum placeholder text generator.
In line “Enter file in which to save the key (/root/.ssh/id_rsa):”
It is asking the path to save the key and default one is normally fine. If default is fine, you can simply press enter. If you want to try alternate path, then you need to specify the same there. Some times this will says like:

You should take a copy of the .ssh folder before making any changes or should know what you are doing. Sending a Yes will make old key (if in use already ) not to work.
In the line “Enter passphrase (empty for no passphrase):” This is an additional security procedure which will ask passphrase each time when you try to login to SSH and that will work as a 2 step verification. But if you need ssh access for any scripting or any other direct works and speedy works, then better to not to have this. Other than scripting or automating the works, we will suggest you to have this for sure.
Full result of the command for reference:
Generating public/private rsa key pair.
Enter fileinwhich to save the key (/root/.ssh/id_rsa):
Created directory '/root/.ssh'.
Enter passphrase (empty for no passphrase):
Enter same passphrase again:
Your identification has been saved in/root/.ssh/id_rsa.
Your public key has been saved in/root/.ssh/id_rsa.pub.
The key fingerprint is:
SHA256:z4nl0d9vJpo/5bdc4gYZh8nnTjHtXB4Se/UqyuyigUI sumesh@Sree
The key's randomart image is:
+---[RSA 2048]----+
. .
. oo.o
.=o=o+
E S o .*oBo
. . * o+.+.=
. . . .o=. =ooo
. . + o*.B
. o. o+oB+
+----[SHA256]-----+
root@Source~$
Step 2 : Copy this created Key Pair to your Destination Server
There are 2 different ways to get this copied to your destination server
- Using the ssh-copy-id command
- Copying the ssh key using normal ssh user/pass as one liner from our local machine or after logging in the server.
2.1 Using the ssh-copy-id command
ssh-copy-id will handle the copy and setup of the key to a remote server in the proper way for you. Once the command is completed you will not need a password for each login. Now you can write all your automated scripts for system admin work without having to enter a password manually and save time on day to day access of systems you use all the time.
First you need to check if there is a command like this and if the command is working and user as which you are trying is having access to this command, then you can use this command to copy the public key to the remote server. This Utility will scan your local account for any rsa public key and will prompt you for the password of the remote user’s account.
Here we are going to copy the root ssh key to the servers root level access. So to get this copied, you need to login / switch to the user for which you have created the key. In this case we are trying root-root connection.
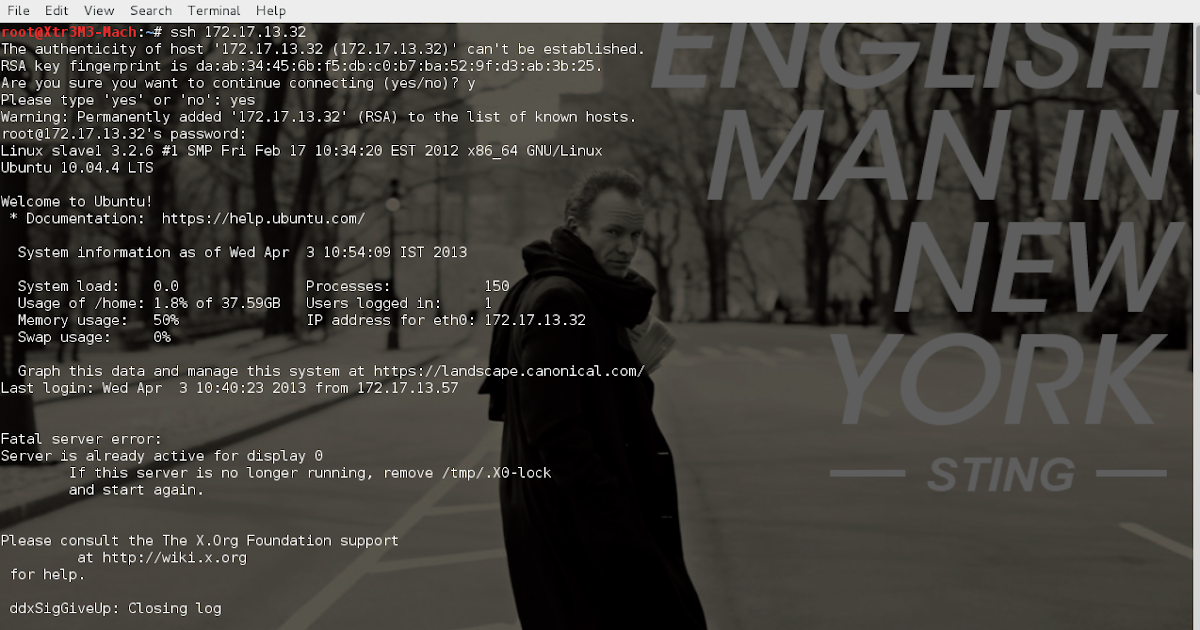
Full output is below and I am adding needed details in between them
The authenticity of host '[192.1.1.19]:1986 ([192.1.1.19]:1986)' can't be established.
ECDSA key fingerprint is SHA256:YYOj54aEJvIle4D2osDiEhuS0NEDImPTiMhHGgDqQFk.
Are you sure you want to continue connecting (yes/no)? yes
If you are using this for the first time, you will get such a response and you need to type yes and then press enter
to filter out any that are already installed
/usr/bin/ssh-copy-id: INFO: 1 key(s) remain to be installed --if you are prompted
now it is to install the new keys
root@192.1.1.19's password:
Enter the password and then press enter.
Generate New Ssh Key Kali Version
Now try logging into the machine, with: “ssh -p ‘1986’ ‘root@192.1.1.19′”
and check to make sure that it is working as expected.
Generate RSA keys with SSH by using PuTTYgen. One effective way of securing SSH access to your cloud server is to use a public-private key pair. This means that a public key is placed on the server and a private key is placed on your local workstation. To generate a set of RSA keys with PuTTYgen: Start the PuTTYgen utility, by double-clicking on its.exe file For Type of key to generate, select RSA In the Number of bits in a generated key field, specify either 2048 or 4096 (increasing the bits makes it harder to crack the key by brute-force methods. To generate the public/private key pair, enter this in the Command Prompt: ssh-keygen At the first prompt, “Enter file in which to save the key,” press Enter to save it in the default location. Ssh rsa generate public key. Sep 06, 2019 Generating your key pair and propagating your public key is simpler than it sounds. Let’s walk through it. Generating the key. The minimum effort to generate a key pair involves running the ssh-keygen command, and choosing the defaults at all the prompts: $ ssh-keygen Generating public/private rsa key. Generating Your SSH Public Key Many Git servers authenticate using SSH public keys. In order to provide a public key, each user in your system must generate one if they don’t already have one. This process is similar across all operating systems.
After this you will be able to login to server without any passwords. Once password less auth is working fine, you can disable the password authentication so that you can lock ssh access to just using ssh keys
2.2 Copying the ssh key using normal ssh user/pass manually
If some how you are not able to get that above command working, I will add the steps so that you can copy the ssh key and setup password less auth from your machine to your server.
To do this we have to manually append the content of your id_rsa.pub file to the /root/.ssh/authorized_keys file on your Destination machine. If you are going to copy the key to root user the location will be /root/.ssh/authorized_keys .
From the Step 1 : you may have seen the below line
Your public key has been saved in /root/.ssh/id_rsa.pub.
This says the public key which you need to copy to the remote server is located in the above file. So you need to copy the content of this file and then copy or paste them in the authorized_keys of the remote server
So do the below steps
Below command will give you the key to be copied:
Generate New Ssh Key Kali File
ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAACAQCqql6MzstZYh1TmWWv11q5O3pISj2ZFl9Hg
H1JLknLLx44+tXfJ7mIrKNxOOwxIxvcBF8PXSYvobFYEZjGIVCEAjrUzLiIxbyCoxVyle7Q+bqgZ
8SeeM8wzytsY+dVGcBxF6N4JS+zVk5eMcV385gG3Y6ON3EG112n6d+SMXY0OEBIcO6x+PnUS
GHrSgpBgX7Ks1r7xqFa7heJLLt2wWwkARptX7udSq05paBhcpB0pHtA1Rfz3K2B+ZVIpSDfki9UV
KzT8JUmwW6NNzSgxUfQHGwnW7kj4jp4AT0VZk3ADw497M2G/12N0PPB5CnhHf7ovgy6nL1ik
rygTKRFmNZISvAcywB9GVqNAVE+ZHDSCuURNsAInVzgYo9xgJDW8wUw2o8U77+xiFxgI5QSZ
X3Iq7YLMgeksaO4rBJEa54k8m5wEiEE1nUhLuJ0X/vh2xPff6SQ1BL/zkOhvJCACK6Vb15mDOeCS
q54Cr7kvS46itMosi/uS66+PujOO+xt/2FWYepz6ZlN70bRly57Q06J+ZJoc9FfBCbCyYH7U/ASsmY0
95ywPsBo1XQ9PqhnN1/YOorJ068foQDNVpm146mUpILVxmq41Cj55YKHEazXGsdBIbXWhcrRf4G
2fJLRcGUr9q8/lERo9oxRm5JFX6TCmj6kmiFqv+Ow9gI0x8GvaQ root@Source
Login to Remote server to which you need to copy this above key and make sure you use the same user to which you need to copy the ssh key. If you need direct root access, copy the key directly to /root/.ssh/ section
Create a folder .ssh if it does not exist
To check if that exists and if not create it using the below commands:
If the folder is not there , then create it with the below command:
root@destination$ touch/root/.ssh/authorized_keys
root@destination:$ echo “ssh-rsa
AAAAB3NzaC1yc2EAAAADAQABAAACAQCqql6MzstZYh1TmWWv11q5O3pISj2ZFl9HgH1JLknLLx44+tXfJ7mIrKNxOOwxI
xvcBF8PXSYvobFYEZjGIVCEAjrUzLiIxbyCoxVyle7Q+bqgZ8SeeM8wzytsY+dVGcBxF6N4JS+zVk5eMcV385gG3Y6ON3
EG112n6d+SMXY0OEBIcO6x+PnUSGHrSgpBgX7Ks1r7xqFa7heJLLt2wWwkARptX7udSq05paBhcpB0pHtA1Rfz3K2B+ZV
IpSDfki9UVKzT8JUmwW6NNzSgxUfQHGwnW7kj4jp4AT0VZk3ADw497M2G/12N0PPB5CnhHf7ovgy6nL1ikrygTKRFmNZI
SvAcywB9GVqNAVE+ZHDSCuURNsAInVzgYo9xgJDW8wUw2o8U77+xiFxgI5QSZX3Iq7YLMgeksaO4rBJEa54k8m5wEiEE1
nUhLuJ0X/vh2xPff6SQ1BL/zkOhvJCACK6Vb15mDOeCSq54Cr7kvS46itMosi/uS66+PujOO+xt/2FWYepz6ZlN70bRly
57Q06J+ZJoc9FfBCbCyYH7U/ASsmY095ywPsBo1XQ9PqhnN1/YOorJ068foQDNVpm146mUpILVxmq41Cj55YKHEazXGsd
BIbXWhcrRf4G2fJLRcGUr9q8/lERo9oxRm5JFX6TCmj6kmiFqv+Ow9gI0x8GvaQroot@Source“ >>
/root/.ssh/authorized_keys
Make sure the permission of the folder is correct one
After this please try login to server from a new terminal and make sure keyless auth is working as expected. Only then disable password authentication in the ssh config.
NOTE: Make double sure you are able to login to server as needed by you (either directly from your machine, or you can login to another user in the remote server and switch to root from that account manually using su or sudo ) and then only disable password auth else there is chances to get root users locked.
If you have any needs you can always contact me for any help and share your comments.