Ssh Rsa Generate Public Key
To generate the missing public key again from the private key, the following command will generate the public key of the private key provided with the -f option. $ ssh-keygen -y -f /.ssh/idrsa /.ssh/idrsa.pub Enter passphrase: The -y option will read a private SSH key file and prints an SSH public key to stdout. The public key part is redirected to the file with the same name as the private key but. Generating Your SSH Public Key Many Git servers authenticate using SSH public keys. In order to provide a public key, each user in your system must generate one if they don’t already have one. This process is similar across all operating systems. Ssh-keygen -t rsa -b 4096 -C 'RSA 4096 bit Keys' Generate an DSA SSH keypair with a 2048 bit private key. Ssh-keygen -t dsa -b 1024 -C 'DSA 1024 bit Keys' Generate an ECDSA SSH keypair with a 521 bit private key. Ssh-keygen -t ecdsa -b 521 -C 'ECDSA 521 bit Keys' Generate an ed25519 SSH keypair- this is a new algorithm added in OpenSSH. Jun 22, 2012 The private key (identification) is now located in /home/ demo /.ssh/idrsa. Step Three—Copy the Public Key. Once the key pair is generated, it’s time to place the public key on the server that we want to use. You can copy the public key into the new machine’s authorizedkeys file with the ssh-copy-id command.

Nov 10, 2011 How to Generate A Public/Private SSH Key Linux 1. Open a terminal. In the next screen, you should see a prompt, asking you for the location to save the key. Next, you will be prompted to enter passphrase. Your public and private SSH key should now be generated. Jul 30, 2015 Different SSH programs generate public keys in different ways, but they all generate public keys in a similar format: ssh-rsa or ssh-dss @ Key-Based SSH Logins. Key-based authentication is the most secure of several modes of authentication usable with OpenSSH, such as plain password.
Overview
Public key authentication is a way of logging into an SSH/SFTP account using a cryptographic key rather than a password.
If you use very strong SSH/SFTP passwords, your accounts are already safe from brute force attacks. However, using public key authentication provides many benefits when working with multiple developers. For example, with SSH keys you can
- allow multiple developers to log in as the same system user without having to share a single password between them;
- revoke a single developer's access without revoking access by other developers; and
- make it easier for a single developer to log in to many accounts without needing to manage many different passwords.
How Public Key Authentication Works
Keys come in pairs of a public key and a private key. Each key pair is unique, and the two keys work together.
These two keys have a very special and beautiful mathematical property: if you have the private key, you can prove you have it without showing what it is. It's like proving you know a password without having to show someone the password.
Public key authentication works like this:
- Generate a key pair.
- Give someone (or a server) the public key.
- Later, anytime you want to authenticate, the person (or the server) asks you to prove you have the private key that corresponds to the public key.
- You prove you have the private key.
You don't have to do the math or implement the key exchange yourself. The SSH server and client programs take care of this for you.
Generate an SSH Key Pair
You should generate your key pair on your laptop, not on your server. All Mac and Linux systems include a command called ssh-keygen that will generate a new key pair.
If you're using Windows, you can generate the keys on your server. Just remember to copy your keys to your laptop and delete your private key from the server after you've generated it.
To generate an SSH key pair, run the command ssh-keygen.
It will look like this when you run it:
You'll be prompted to choose the location to store the keys. The default location is good unless you already have a key. Press Enter to choose the default location.
Next, you'll be asked to choose a password. Using a password means a password will be required to use the private key. It's a good idea to use a password on your private key.
After you choose a password, your public and private keys will be generated. There will be two different files. The one named id_rsa is your private key. The one named id_rsa.pub is your public key.
You'll also be shown a fingerprint and 'visual fingerprint' of your key. You do not need to save these.
Configure an SSH/SFTP User for Your Key
Method 1: Using ssh-copy-id
Now that you have an SSH key pair, you're ready to configure your app's system user so you can SSH or SFTP in using your private key.
To copy your public key to your server, run the following command. Be sure to replace 'x.x.x.x' with your server's IP address and SYSUSER with the name of the the system user your app belongs to.
Method 2: Manual Configuration
If you don't have the ssh-copy-id command (for example, if you are using Windows), you can instead SSH in to your server and manually create the .ssh/authorized_keys file so it contains your public key.
First, run the following commands to make create the file with the correct permissions.
Next, edit the file .ssh/authorized_keys using your preferred editor. Copy and paste your id_rsa.pub file into the file.
Log In Using Your Private Key
You can now SSH or SFTP into your server using your private key. From the command line, you can use:
If you didn't create your key in the default location, you'll need to specify the location:
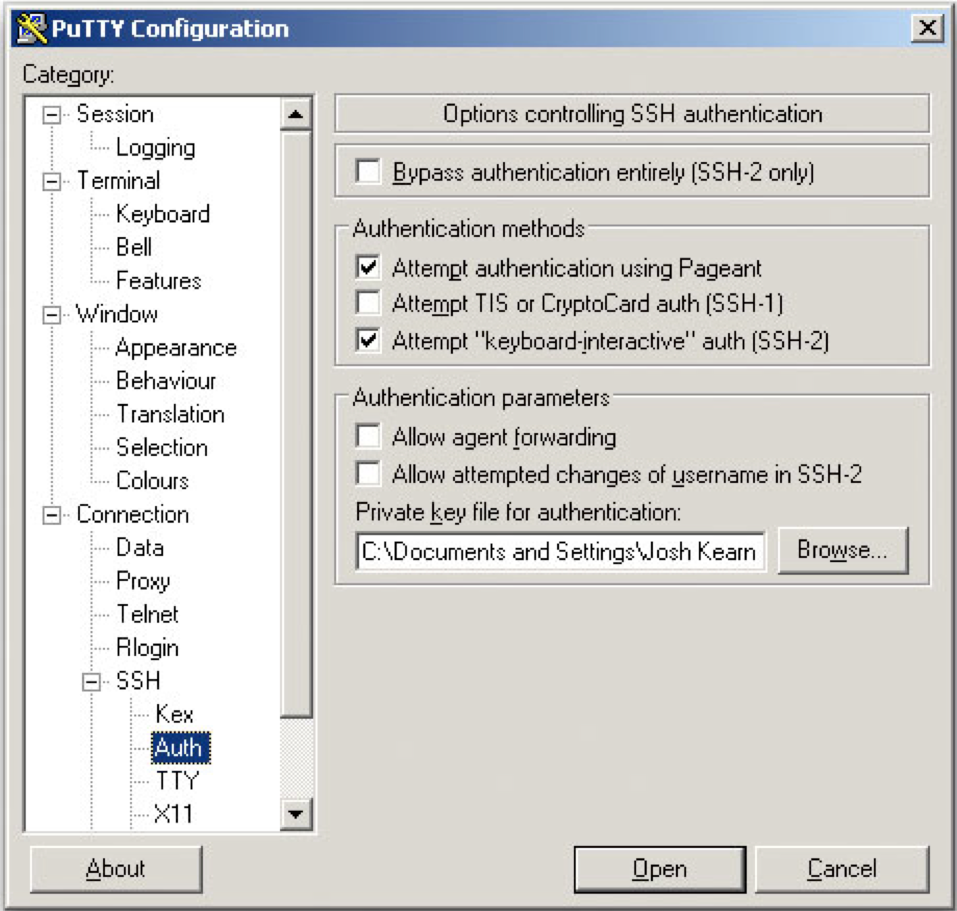
If you're using a Windows SSH client, such as PuTTy, look in the configuration settings to specify the path to your private key.
Ssh Rsa Generate Public Key From Private Key
Granting Access to Multiple Keys
The .ssh/authorized_keys file you created above uses a very simple format: it can contain many keys as long as you put one key on each line in the file.
If you have multiple keys (for example, one on each of your laptops) or multiple developers you need to grant access to, just follow the same instructions above using ssh-copy-id or manually editing the file to paste in additional keys, one on each line.
When you're done, the .ssh/authorized_keys file will look something like this (don't copy this, use your own public keys):
Additional Information
Retrieve Your Public Key from Your Private Key
The following command will retrieve the public key from a private key:
This can be useful, for example, if your server provider generated your SSH key for you and you were only able to download the private key portion of the key pair.
Note that you cannot retrieve the private key if you only have the public key.
Correcting Permissions on the .ssh Directory
The instructions in this article will create your server's .ssh directory and .ssh/authorized_keys file with the correct permissions. However, if you've created them yourself and need to fix permissions, you can run the following commands on your server while SSH'd in as your app's system user.
Disabling Password Authentication
NOTE: When changing anything about the way SSH is accessed(ports, authentication methods, et cetera), it is very strongly recommended to leave an active root SSH session open until everything is working as intended. This ensures you have a way to revert changes in the event something goes wrongand logins are not working properly.
As an extra security precaution, once you have set up SSH keys, you may wish to disable password authentication entirely. This will mean no users will be able to log into SSH or SFTP without SSH keys. Anyone entering a password will receive a message like:
Or:
Disabling password authentication is an excellent way to improve server security. Please see our guide here for the steps to accomplish this goal.
Then, test whether you're able to log in with a password by opening a new SSH or SFTP session to the server. Passwords should not be able to be used and, if everything has been done correctly, an error will be issued when someone tries to use a password. Unless this setting is changed back to allow password authentication, no users will be able to log in without an SSH key set up.
You generate an SSH key through macOS by using the Terminal application. Once you upload a valid public SSH key, the Triton Compute Service uses SmartLogin to copy the public key to any new SmartMachine you provision.
Joyent recommends RSA keys because the node-manta CLI programs work with RSA keys both locally and with the ssh agent. DSA keys will work only if the private key is on the same system as the CLI, and not password-protected.
About Terminal
Terminal is the terminal emulator which provides a text-based command line interface to the Unix shell of macOS.
To open the macOS Terminal, follow these steps:
- In Finder, choose Utilities from the Applications folder.
- Find Terminal in the Utilities listw.
- Open Terminal.
The Terminal window opens with the commandline prompt displaying the name of your machine and your username.
Generating an SSH key
An SSH key consists of a pair of files. One is the private key, which should never be shared with anyone. The other is the public key. The other file is a public key which allows you to log into the containers and VMs you provision. When you generate the keys, you will use ssh-keygen to store the keys in a safe location so you can bypass the login prompt when connecting to your instances.
Generate Rsa Public Key
To generate SSH keys in macOS, follow these steps:
Enter the following command in the Terminal window.
The secret key is a unique piece of information that is used to compute the HMAC and is known both by the sender and the receiver of the message. This key will vary in length depending on the algorithm that you use. I use Bouncy Castle for the implementation. You can also use this page in HTTPS (SSL). Online HMAC hash generator: HMAC-MD5, HMAC-SHA A keyed-hash message authentication code (HMAC) uses a cryptographic hash function (MD5, SHA-1, SHA-512 ) and a secret cryptographic key to verify both the data integrity and the authentication of a message. RandomKeygen is a free mobile-friendly tool that offers randomly generated keys and passwords you can use to secure any application, service or device. KEY RandomKeygen - The Secure Password & Keygen Generator. With HMAC-SHA signature you don't need a public key. There is one secret key shared by the server (service) and the client that is used to compute the signature. Per the question on the security site referenced above, make sure you have different keys for each client. HMAC(Hash-based message authentication code) is a message authentication code that uses a cryptographic hash function such as SHA-256, SHA-512 and a secret key known as a cryptographic key. HMAC is more secure than any other authentication codes as it contains Hashing as well as MAC. Below is a free online tool that can be used to generate HMAC authentication code. We can generate hmac-sha256. Generate secret key for hmac.
This starts the key generation process. When you execute this command, the
ssh-keygenutility prompts you to indicate where to store the key.Press the ENTER key to accept the default location. The
ssh-keygenutility prompts you for a passphrase.- Type in a passphrase. You can also hit the ENTER key to accept the default (no passphrase). However, this is not recommended.
You will need to enter the passphrase a second time to continue.
After you confirm the passphrase, the system generates the key pair.
Your private key is saved to the id_rsa file in the .ssh directory and is used to verify the public key you use belongs to the same Triton Compute Service account.
| Never share your private key with anyone! |
|---|
Your public key is saved to the id_rsa.pub;file and is the key you upload to your Triton Compute Service account. You can save this key to the clipboard by running this:
Importing your SSH key
Now you must import the copied SSH key to the portal.
- After you copy the SSH key to the clipboard, return to your account page.
- Choose to Import Public Key and paste your SSH key into the Public Key field.
- In the Key Name field, provide a name for the key. Note: although providing a key name is optional, it is a best practice for ease of managing multiple SSH keys.
- Add the key. It will now appear in your table of keys under SSH.
Create Rsa Ssh Key
Troubleshooting
You may see a password prompt like this:
This is because:
- You did not enter the correct passphrase.
- The private key on your Macintosh (
id_rsa) does not match the public key stored with your Triton Compute Service account. - The public key was not entered correctly in your Triton account.
What are my next steps?
Right in the portal, you can easily create Docker containers, infrastructure containers, and hardware virtual machines.
In order to use the Terminal to create instances, set up triton and CloudAPI as well as the triton-docker commandline tool.