Generate Csr Without Private Key
Important: This example is intended to provide general guidance to IT professionals who are experienced with SSL requirements and configuration. The procedure described in this article is just one of many available methods you can use to generate the required files. The process described here should be treated as an example and not as a recommendation.
Mar 09, 2020 Microsoft Office 2013 Product Key Generator has been a part of many lives for decades. It facilitates professionals, businesses, student and individuals for personal purposes. There have been many versions created, each more enhanced than the next. Microsoft Office 2013 follows Microsoft Office 10 and precedes Microsoft Office 2016. Mar 02, 2020 Microsoft Office Professional 2013 Crack is stylish and advanced software. It is compatible both for 32 bit or 64-bit operating system. In this software, you can easily edit any Pdfs. Microsoft office 2013 Product Key is and safe and updated version. Free microsoft office 2013 activation. Microsoft Office 2013 Product Key Generator is an excellent application which gives you better workplace. It includes plenty of amazing tools & features. In Microsoft Office 2013, a computer must have utility software pack. It serves as the foundation for document control and has multiple purposes. What is the Microsoft Office 2013 Product Key? Microsoft Office 2013 product key is a 25-digit code that’s required to activate a copy of MS Office 2013. The product license key code looks like this: XXXXX-XXXXX-XXXXX-XXXXX-XXXXX. If you don’t provide a working key product code, you will not be able to use Microsoft Office 2013.
When you configure Tableau Server to use Secure Sockets Layer (SSL) encryption, this helps ensure that access to the server is secure and that data sent between Tableau Server and Tableau Desktop is protected.
What I am trying to do is, create a CSR and with a private key that is password protected (the key). In OpenSSL I can create a private key with a password like so: openssl genrsa -des3 -out privkey.pem 2048 Is there some way I can use the key I just created and generate a CSR using the key? CSRs are signed using the private key to prevent tampering in transit to the CA. Accordingly, you need the private key to create one. It is possible to create a CSR that has no signature, but such constructions are not common and the openssl binary itself has no provisions for creating them. In this article you’ll find how to generate CSR (Certificate Signing Request) using OpenSSL from the Linux command line, without being prompted for values which go in the certificate’s subject field. Below you’ll find two examples of creating CSR using OpenSSL. In the first example, i’ll show how to create both CSR and the new private key in one command. Apr 12, 2020 Now to create SAN certificate we must generate a new CSR i.e. Certificate Signing Request which we will use in next step with openssl generate csr with san command line. root@centos8-1 certs# openssl req -new -key server.key.pem -out server.csr You are about to be asked to enter information that will be incorporated into your certificate request. Before you can order an SSL certificate, it is recommended that you generate a Certificate Signing Request (CSR) from your server or device. Learn more about SSL certificates » A CSR is an encoded file that provides you with a standardized way to send DigiCert your public key as well as some. How to generate a CSR code on a Windows-based server without IIS Manager. What if we need to install an SSL certificate for the service other than IIS and there is no IIS Manager installed on the Windows server? How one can generate a CSR code in this situation? Luckily, there are a few workarounds available. MMC (Microsoft Management Console). How to Generate a CSR for Microsoft IIS 8 The following instructions will guide you through the CSR generation process on Microsoft IIS 8. To learn more about CSRs and the importance of your private key, reference our Overview of Certificate Signing Request article.
Looking for Tableau Server on Linux? See Example: SSL Certificate - Generate a Key and CSR.
Tableau Server uses Apache, which includes OpenSSL. You can use the OpenSSL toolkit to generate a key file and Certificate Signing Request (CSR) which can then be used to obtain a signed SSL certificate.
Steps to generate a key and CSR
To configure Tableau Server to use SSL, you must have an SSL certificate. To obtain the SSL certificate, complete the steps:
- Generate a key file.
- Create a Certificate Signing Request (CSR).
- Send the CSR to a certificate authority (CA) to obtain an SSL certificate.
- Use the key and certificate to configure Tableau Server to use SSL.
You can find additional information on the SSL FAQ page on the Apache Software Foundation website.
Configure a certificate for multiple domain names
Tableau Server allows SSL for multiple domains. To set up this environment, you need to modify the OpenSSL configuration file, openssl.conf, and configure a Subject Alternative Name (SAN) certificate on Tableau Server. See For SAN certificates: modify the OpenSSL configuration file below.
Set the OpenSSL configuration environment variable (optional)
Generate Csr Private Key
To avoid using the -config argument with every use of openssl.exe, you can use the OPENSSL_CONF environment variable to ensure that the correct configuration file is used and all configuration changes made in subsequent procedures in this article produce expected results (for example, you must set the environment variable to add a SAN to your certificate).
Open the Command Prompt as an administrator, and run the following command:
set OPENSSL_CONF=c:Program FilesTableauTableau Serverpackagesapache.<version_code>confopenssl.cnf
Generate Csr Without Private Key Data
Notes:
When setting the Open SSL configuration environment variable, do not enclose the file path with quotation marks.
If you are using a 32-bit version of Tableau Server on a 64-bit computer, run the
set OPENSSL_CONF=c:Program Files (x86)TableauTableau Serverpackagesapache.<version_code>confopenssl.cnfcommand instead.
Generate a key
Generate a key file that you will use to generate a certificate signing request.
Open the Command Prompt as an administrator, and navigate to the Apache directory for Tableau Server. For example, run the following command:
cd C:Program FilesTableauTableau Serverpackagesapache.<version_code>binRun the following command to create the key file:
openssl.exe genrsa -out <yourcertname>.key 4096Note: This command uses a 4096-bit length for the key. You should choose a bit length that is at least 2048 bits because communication encrypted with a shorter bit length is less secure. If a value is not provided, 512 bits is used.
Create a certificate signing request to send to a certificate authority
Use the key file you created in the procedure above to generate the certificate signing request (CSR). You send the CSR to a certificate authority (CA) to obtain a signed certificate.
Important: If you want to configure a SAN certificate to use SSL for multiple domains, first complete the steps in For SAN certificates: modify the OpenSSL configuration file below, and then return to here to generate a CSR.
Run the following command to create a certificate signing request (CSR) file:
openssl.exe req -new -key yourcertname.key -out yourcertname.csrIf you did not set the OpenSSL configuration environment variable,
OPENSSL_CONF, you might see either of the following messages:An error message about the config information being unable to load. In this case, retype the command above with the following parameter:
-config .confopenssl.cnf.A warning that the
/usr/local/ssldirectory cannot be found. This directory does not exist on Windows, and you can simply ignore this message. The file is created successfully.
To set an OpenSSL configuration environment variable, see Set the OpenSSL configuration environment variable (optional) section in this article.
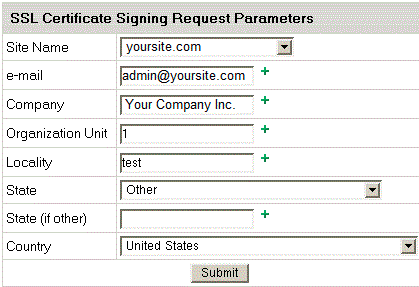
When prompted, enter the required information.
Note: For Common Name, type the Tableau Server name. The Tableau Server name is the URL that will be used to reach the Tableau Server. For example, if you reach Tableau Server by typing
tableau.example.comin the address bar of your browser, thentableau.example.comis the common name. If the common name does not resolve to the server name, errors will occur when a browser or Tableau Desktop tries to connect to Tableau Server.
Send the CSR to a certificate authority to obtain an SSL certificate
Send the CSR to a commercial certificate authority (CA) to request the digital certificate. For information, see the Wikipedia article Certificate authority and any related articles that help you decide which CA to use.
Use the key and certificate to configure Tableau Server
When you have both the key and the certificate from the CA, you can configure Tableau Server to use SSL. For the steps, see Configure External SSL.
For SAN certificates: modify the OpenSSL configuration file
In a standard installation of OpenSSL, some features are not enabled by default. To use SSL with multiple domain names, before you generate the CSR, complete these steps to modify the openssl.cnf file.
Open Windows Explorer and browse to the Apache conf folder for Tableau Server.
For example:
C:Program FilesTableauTableau Server<version_code>apacheconfOpen openssl.cnf in a text editor, and find the following line:
req_extensions = v3_reqThis line might be commented out with a hash sign (#) at the beginning of the line.
If the line is commented out, uncomment it by removing the # and space characters from the beginning of the line.
Move to the [ v3_req ] section of the file. The first few lines contain the following text:
# Extensions to add to a certificate request
basicConstraints = CA:FALSE
keyUsage = nonRepudiation, digitalSignature, keyEnciphermentAfter the keyUsage line, insert the following line:
subjectAltName = @alt_namesIf you’re creating a self-signed SAN certificate, do the following to give the certificate permission to sign the certificate:
Add the
cRLSignandkeyCertSignto the keyUsage line so it looks like the following:keyUsage = nonRepudiation, digitalSignature, keyEncipherment, cRLSign, keyCertSignD2 key generator for median xl. He's found at one end of the four-pointed, the lowest of the three Halls levels reached through 's portal in, in. One of each.The Key of Destruction is required to open the first in the and can only be found from certain boss monsters, and only on Hell difficulty.Get the from, the from, and the from. It's a good idea to have 3 of each key before beginning the second stage of the Pandemonium Event, for reasons explained in the article.The keys look identical, and can only be discerned between by hovering on them to see their name.Key of Destruction sometimes drops this key, but only on.
After the keyUsage line, add the following line:
subjectAltName = @alt_names
In the [alt_names] section, provide the domain names you want to use with SSL.
DNS.1 = [domain1]
DNS.2 = [domain2]
DNS.3 = [etc]The following image shows the results highlighted, with placeholder text that you would replace with your domain names.
Save and close the file.
Complete the steps in Create a certificate signing request to send to a certificate authority section, above.
Additional information
If you prefer to use a different version of OpenSSL, you can download it from Open SSL for Windows.