Algorithms For Generating Symmetric Key
10.2.1: Some Variations on the KDC Approach to Key Distribution. ItisnotpracticaltohaveasingleKDCserviceverylargenetworks or network of networks. One can think of KDC’s organized hierarchically, with each lo- cal network serviced by its own KDC, and a group of networks serviced by a more global KDC, and so on. The Diffie-Hellman algorithm is being used to establish a shared secret that can be used for secret. Communications while exchanging data over a public network using the elliptic curve to generate points and get the secret key using the parameters.
Creating and managing keys is an important part of the cryptographic process. Symmetric algorithms require the creation of a key and an initialization vector (IV). The key must be kept secret from anyone who should not decrypt your data. The IV does not have to be secret, but should be changed for each session. Asymmetric algorithms require the creation of a public key and a private key. The public key can be made public to anyone, while the private key must known only by the party who will decrypt the data encrypted with the public key. This section describes how to generate and manage keys for both symmetric and asymmetric algorithms.
How to Generate a Symmetric Key by Using the pktool Command. Some applications require a symmetric key for encryption and decryption of communications. In this procedure, you create a symmetric key and store it. If your site has a random number generator, you can use the generator to create a random number for the key. Modern cryptographic systems include symmetric-key algorithms (such as DES and AES) and public-key algorithms (such as RSA). Symmetric-key algorithms use a single shared key; keeping data secret requires keeping this key secret. Public-key algorithms use a public key and a private key. Two types of encryption algorithms can be used by the encryption key server: symmetric algorithms and asymmetric algorithms. Symmetric, or secret key encryption, uses a single key for both encryption and decryption. Symmetric key encryption is used for encrypting large amounts of data efficiently. 256-bit AES keys are symmetric keys. Symmetric encryption algorithms are used to encrypt data. Asymmetric encryption algorithms are used to decrypt data. Symmetric encryption algorithms use pre-shared keys. Asymmetric encryption algorithms use different keys to encrypt and decrypt data. Symmetric encryption algorithms use pre-shared keys. Alternatively, you may want to derive a key from some other source. A Key Derivation Function (KDF) is a function that transforms some input into a key. GPG uses a Password-Based KDF (PBKDF, also known as a 'password hash') to transform a password into a symmetric key.
Symmetric Keys
The symmetric encryption classes supplied by the .NET Framework require a key and a new initialization vector (IV) to encrypt and decrypt data. Whenever you create a new instance of one of the managed symmetric cryptographic classes using the parameterless constructor, a new key and IV are automatically created. Anyone that you allow to decrypt your data must possess the same key and IV and use the same algorithm. Generally, a new key and IV should be created for every session, and neither the key nor IV should be stored for use in a later session.
Key generator call of duty 4 modern warfare. Meanwhile, Hovec Sawmill is a brand new map described as a “three-lane map with a balance of mid to long-range sightlines.”“A sleepy farming village is under peril, as its main sawmill building has caught fire. Among the new updates, three new Modern Warfare maps for multiplayer have been revealed.The maps called Talsik Backlot, Hovec Sawmill and Aniyah Incursion will all be available for free in time for the latest season.Talisk Backlot, as Activision noted, should be a familiar map to “Call of Duty 4: Modern Wafare” fans. After all, it is a remaster of the said map that features areas that are good for close-quarter battles and long-range sniping battles.
To communicate a symmetric key and IV to a remote party, you would usually encrypt the symmetric key by using asymmetric encryption. Sending the key across an insecure network without encrypting it is unsafe, because anyone who intercepts the key and IV can then decrypt your data. For more information about exchanging data by using encryption, see Creating a Cryptographic Scheme.
Generating a 4096 bit rsa private key. The only requirement for secure encryption in RSA is that exponentiating the message m to the eth power 'wraps the modulus', i.e. So in practice values of e as small as 3 (2 bits) have been used. There is no requirement for what bit size e is.
The following example shows the creation of a new instance of the TripleDESCryptoServiceProvider class that implements the TripleDES algorithm.
Symmetric Algorithms
When the previous code is executed, a new key and IV are generated and placed in the Key and IV properties, respectively.
Sometimes you might need to generate multiple keys. In this situation, you can create a new instance of a class that implements a symmetric algorithm and then create a new key and IV by calling the GenerateKey and GenerateIV methods. The following code example illustrates how to create new keys and IVs after a new instance of the symmetric cryptographic class has been made.
When the previous code is executed, a key and IV are generated when the new instance of TripleDESCryptoServiceProvider is made. Another key and IV are created when the GenerateKey and GenerateIV methods are called.
Asymmetric Keys
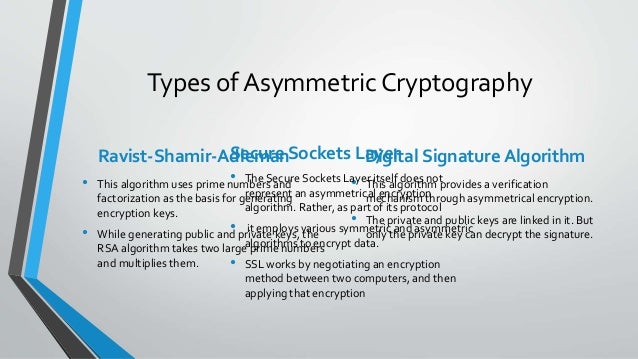
The .NET Framework provides the RSACryptoServiceProvider and DSACryptoServiceProvider classes for asymmetric encryption. These classes create a public/private key pair when you use the parameterless constructor to create a new instance. Asymmetric keys can be either stored for use in multiple sessions or generated for one session only. While the public key can be made generally available, the private key should be closely guarded.
Algorithms For Generating Symmetric Key And C
A public/private key pair is generated whenever a new instance of an asymmetric algorithm class is created. After a new instance of the class is created, the key information can be extracted using one of two methods:
The ToXmlString method, which returns an XML representation of the key information.
The ExportParameters method, which returns an RSAParameters structure that holds the key information.
Both methods accept a Boolean value that indicates whether to return only the public key information or to return both the public-key and the private-key information. An RSACryptoServiceProvider class can be initialized to the value of an RSAParameters structure by using the ImportParameters method.
Asymmetric private keys should never be stored verbatim or in plain text on the local computer. If you need to store a private key, you should use a key container. For more on how to store a private key in a key container, see How to: Store Asymmetric Keys in a Key Container.
The following code example creates a new instance of the RSACryptoServiceProvider class, creating a public/private key pair, and saves the public key information to an RSAParameters structure.